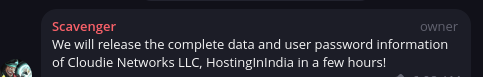
Cloudie Networks, LLC. Data Leakage
 Abdullah
Hosting ProviderOG
Abdullah
Hosting ProviderOG
Just got this email. WHMCSec security team (?) anyone knows who that is.
I saw someone mention here about LetBox staff stating their system was compromised and all VMs need to be reinstalled. So this seems credible.
Dear name
Hello and Merry Christmas.
We are the WHMCSec security team. Recently we broke into Cloudie and obtained complete data.
We tried to communicate with him in a friendly manner and offered him $200 to help him improve security and avoid data leakage.
But he replied to us that he doesn't care about the security of user data.
And lied to you, claiming that the data was not leaked
Therefore we decided to release its complete database SQL DUMP within 24 hours, please join our Telegram group to learn more
[redacted]
Our goal is to clean up all hosting providers who are not responsible for customer data
In addition, we will also release data on SmartHost, LetBox, etc. in the near future.


Comments
Checks inbox.
For staff assistance or support issues please use the helpdesk ticket system at https://support.lowendspirit.com/index.php?a=add
Extortion season.
Three similar emails received at MetalVPS. Plus also an invoice email for $0 and a payment confirmation email. That's 5 emails all together.
Checking the headers on two of the emails showed different sending MTAs. I haven't checked the other three emails.
Unfortunately I don't have a Telegram account. Maybe WHMCSec will send further email updates. Or maybe someone will post here.
@Cloudie Hope all is okay! Best wishes!
I hope everyone gets the servers they want!
They released the whmcs SQL dump some minutes ago. I hope most people don't re-use same details everywhere!
https://webhorizon.net
Of course people practice good basic OPSEC! This is the Internet...oh.
They claim their goal is noble, but I don't think that dumping user data is a noble deed.
My long-winded drivel on security ethics is here, at 11 minutes (the link should start right there):
Relja of House Novović, the First of His Name, King of the Plains, the Breaker of Chains, WirMach Wolves pack member
BikeGremlin's web-hosting reviews
I guess that means the emails I received could be from different people because the database is public now.
Still hope everything goes okay for @Cloudie! Sending him best wishes!
I hope everyone gets the servers they want!
Change your passwords, boys.
Taking a dump is a noble deed no matter the context
———-
blog | exploring visually |
Please change your passwords, just checked the dump.
My details, and my friend's details were present.
Stay Safe, and Stay Strong @Cloudie!
and Fuck WHMCSservices/WHMCS
Very honorable and trustworthy offer!
Doubt.
Ah, so noble. They refused your untrustworthy blackmail, so you released data compromising hundreds of innocent third party customers. I hope not a single host ever gives into these skids. They'll have you bent over their knee forever, they'll never actually destroy the data, and anytime they need a little refill they'll come shaking their little cup for $200 as a you'll be a known pay pig.
I was already leaked by multiple multinational billion dollar companies (ala Equifax, with more damning personal data) 6+ years ago. Why don't you go clean them up instead of some low end hosts?
I'll keep it as clean as I can, but I really hope antics of some lowlife like this doesn't have much material effect overall.
NVMe VPS | Ryzen 7950X VDS | Dedicated Servers -- Crunchbits.com
do you have the downloadlink to the dump?
i would make a joke but its on cloudies network
youtube.com/watch?v=k1BneeJTDcU
Check dm's
Not looking good is it
THAT IS WHY I ALWAYS USE FAKE DATA AND RANDOMLY GENERATED PASSWORD!
you guys should also do the same. ignore any host that mandatory require you to give them real personal data, they are just trying to feed you to crocodiles
Host-C - VPS Services Provider - AS211462
"If there is no struggle there is no progress"
Good reminder to use unique passwords everywhere (use a password manager).
With how frequent data breaches are these days (to the point where I almost feel desensitized), there's no reason not to.
Website: thomassen.sh
Most generalizations are wrong... is a generalization itself. LOL
Relja of House Novović, the First of His Name, King of the Plains, the Breaker of Chains, WirMach Wolves pack member
BikeGremlin's web-hosting reviews
Any response from Cloudie Networks yet?
They had a notice up a few weeks ago.
https://my.cloudie.sh/index.php?rp=/announcements/4/URGENT-SecurityorPayment-Invalidation-Notice-Action-Required.html
I have not seen the dump file, but assuming that the passwords are hashed and salted, I think it won't be a trivial task for someone to derive the original password from the hash? (Not a security expert here, so I might be wrong)
But yeah, one should still change the password.
It's quite ridiculous that an extortion group calls themselves "Security Team".
Lots of them are called that. Many stresser/booters ran by groups of kids are called that too. Just a term used in that space.
ExtraVM
Its all bcrypt so its pretty secure if you used a strong password. But some rules that @Decicus and @selalumenang talked about:
1. Use unique passwords for every single thing
2. Avoid KYC
Dammit, now I'll have to switch to hunter3 everywhere.
OGF says Cloudie's Discord mods are deleting mentions who bring it up in their chat, and nothing has been sent to their customers from Cloudie yet.
I had someone ping me privately to inform me my details were in the DB. (Well, IncogNET company details). I can confirm it was. (My first/last, business name, business address, business phone number, and my VPN IP)
[ IncogNET LLC ] - Privacy By Design
We believe that privacy and freedom of expression are two very important things, so we offer solutions to accessing and publishing content safely.
[ USA: Liberty Lake, WA | Kansas City, MO | Allentown, PA ] [EU: Naaldwijk, NL ] [ CL Shared | KVM VPS | VPN | Dedicated Servers | Domain Names ]
From what I’ve seen they’ll have the code from configuration.php which is all that is needed to at least turn service passwords into plain text. So it’s not just billing passwords you need to change.
Also email history in WHMCS may contain passwords generated for new services in plain text. For hosts who never changed it in email templates (not sure if WHMCS changed it themselves later), email history at least used to contain plain text passwords written by the user on registration.
Do everything as though everyone you’ll ever know is watching.
Cloudie sent out an email on Dec 16th when the breach happened. The email indicated that no personal or payment data had been breached, but I guess he thought that at the time. He's still probably not awake which is why an email hasn't probably been sent out, it doesn't make sense to not send out an email.
I am a representative of Advin Servers
Yes, and in that email it says "To reiterate, we have no reason to believe that any personal or payment data has been breached..."
Personal details have been breached.
[ IncogNET LLC ] - Privacy By Design
We believe that privacy and freedom of expression are two very important things, so we offer solutions to accessing and publishing content safely.
[ USA: Liberty Lake, WA | Kansas City, MO | Allentown, PA ] [EU: Naaldwijk, NL ] [ CL Shared | KVM VPS | VPN | Dedicated Servers | Domain Names ]